SECURING THE DIGITAL SUPPLY CHAIN
Ensuring a secure supply chain is a necessary precondition in today’s world of commerce. The digital supply chain has emerged as the weakest link...
Know Microsegmentation: A Security Technique
Cause that lead to birth of microsegmentation-
A reknown research shows that more than 30 percent of data center issues are caused by cyber attacks,...
New SECORA Pay brand: one-stop-offering for fast and easy production of payment cards and...
EMV-compliant payment solutions face growing demand worldwide – with a clear path towards contactless and multifunctional use to increase user convenience. Under the brand...
Matrix Security Solutions for Efficient People Management
La Maison Royale, Nairobi, is a 4-star superior boutique business hotel with a “French taste”, State-of-the-art facility and close to the entertainment...
Two-year study explores the roles of information security leaders and how they are affected...
Synopsys, Inc. today published the inaugural CISO Report, the result of a two-year data-driven study exploring the roles of information security leaders and the organizational...
Sequitur Labs Foresees Increased Need for Device Security in 2022
Growth in IoT market, increasing focus on device security & rise in malicious attacks among key factors driving adoption of essential protection...
Matrix Project Series 5MP Bullet Cameras
Matrix introduces its Matrix Project Series 5MP Bullet Cameras which are designed for serious outdoor deployments. The cameras are powered by Sony...
Smart Cards Operating System for Smart Card Applications
In cooperation with Infineon Technologies AG, TrustSEC has launched its new advanced Smart Cards Operating System (OS) BIO-SLCOS for Smart Card Applications....
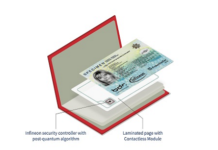
Infineon, German Federal Printing Office & Fraunhofer demonstrated Electronic Passport Security for the Quantum...
Electronic Passport Security for Quantum Computer Era
Quantum computers could become a serious threat to the security of...
Securing 5G from malware, phishing, surveillance and other attack vectors
AdaptiveMobile Security today published a comprehensive blueprint on how to secure SMS on 5G Networks. The research outlines how SMS operates on...