
Recent years have seen an increasing degree of IoT adoption in a variety of industrial fields, and as IoT devices, such as sensors and manufacturing equipment, have been connected to the network, cases of these IoT devices being damaged by malware attacks have occurred worldwide. This has created an urgent need for security countermeasures for IoT devices.
In many cases, however, IoT devices do not support anti-virus software due to CPU, memory, or OS restrictions, and even if anti-virus software is deployed, often software updates that require the device to be rebooted are not executed as the IoT device cannot be stopped while in operation. Due to these factors, the current situation is that many IoT devices are operating with insufficient security measures.
Issues
In light of these problems, various consortiums and network device vendors have proposed measures using gateways to separate the network the IoT devices are connected to from the networks ordinary devices, such as PCs and servers, are connected to (Figure 1). This means that the gateway can protect the devices from cyberattacks from outside networks, but because cyberattacks can be conducted without going through the gateway if a devices infected with malware is connected inside the network the IoT devices are connected to, it was not possible to protect them from cyberattacks from infected devices.
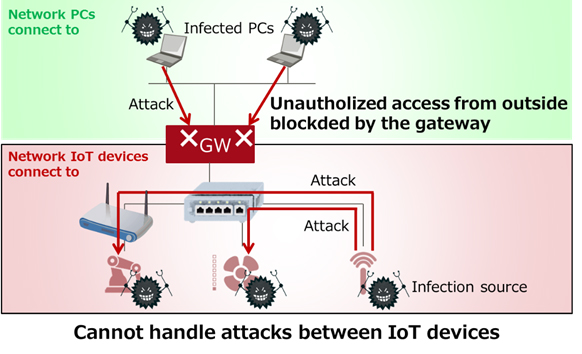 Figure 1: Existing technology: Network separation by a gateway
Figure 1: Existing technology: Network separation by a gateway
About the Newly Developed Technology
Now, Fujitsu Laboratories has developed technology that can collect operating information about IoT devices and network devices from gateway devices, deduce the topology(1) of the network the IoT devices are connected to, and appropriately control the network devices based on this information (Figure 2). With this technology, IoT devices communicating along routes not accounted for in the topology can be treated as unauthorized devices, enabling the technology to minimize the impact of cyberattacks by making those IoT devices unable to communicate with other IoT devices.
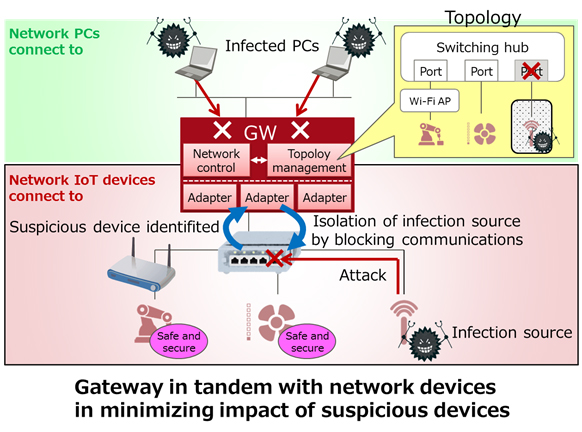 Figure 2: Newly developed method
Figure 2: Newly developed method
Features of the Newly Developed Technology
1. Topology management technology supporting devices with a variety of interfaces
This technology collects information from IoT devices and network devices about adjacent devices in a variety of formats, and then deduces the topology of the entire IoT network as it changes in real time. Because the different devices use a variety of interfaces having respective communication methods and data formats, this topology deduction is enabled by converting them all to a standardized interface in the gateway. With this technology, when IoT devices request an authorized communication route, the technology can collect the actual communication route from the network devices, discovering both unauthorized communications generated by cyberattacks and other issues, as well as the suspicious IoT devices that caused them, by comparing the authorized route with the actual route.
2. Network control technology that blocks communications from suspicious devices
Gateways can block communications between suspicious devices and other devices by controlling the network devices along the route using topology information. Because some devices use wireless, rather than wired connections, it is essential to control the appropriate network device, in a situation where communication pathways change moment to moment, and sometimes communications stop altogether. With this technology, it is possible to block communications by suspicious devices while minimizing the impact on communications of ordinary devices by selecting network devices while taking into consideration changes in topology and device status, and controlling those network devices per the connected device or a group of devices.
Effects
In a simulation using fake malware, Fujitsu Laboratories operated gateways equipped with this technology in coordination with existing network devices, and confirmed that this technology could block communications from suspicious devices. The results showed that this technology could minimize the impact of cyberattacks when installed in gateways.
With this technology, it will be possible to provide secure operations using existing setups, without exchanging or deploying new IoT devices with security countermeasures in sites such as factories, which require the continued operation of production equipment with long service lifespans.
Future Plans
Fujitsu Laboratories aims to commercialize this technology during fiscal 2018 as a gateway feature in the Fujitsu Network Virtuora series of network products. In addition, it will continue to develop the technology, not just for the manufacturing industry, such as factories, but with a view toward expansion into a variety of industrial areas that require safe and secure management of IoT system operations.
For more information, please see www.fujitsu.com.


















