element14 Announces Spy Nerd Design Challenge
Community members are encouraged to design a security or spy related project
element14, an Avnet community, recently launched the Spy...
AAEON Systems Leverage Greater Security Benefits from Partnership with Allxon
AAEON, continues to grow their partnership with Allxon. Allxon recently announced their partnership with Trend Micro to deliver industry-leading cybersecurity software for...
Trend Micro launches its first Cloud One Data Center in India
The move enables enterprises to securely adopt a SaaS-based security framework
Trend Micro Incorporated announced the launch of its Cloud...
Hackers target home Wi-Fi routers to steal data
In this article, a digital privacy expert explains how Wi-Fi routers get hacked nowadays and what users can do to protect themselves.
Internet of Things (IoT) Market segment is projected to reach USD $1.5 trillion by...
Driven by increased adoption of smart sensors integrated into connected devices, the Internet of Things market segment is projected to reach USD...
Synopsys Advances Application Security Testing for Developers with Rapid Scan
New Rapid Scan Capabilities in Coverity SAST & Black Duck SCA Help Development Teams Secure Cloud-native Applications as Fast as They Write...
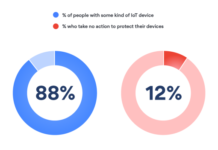
Research: Many users do nothing to protect their smart devices
Almost 88% of people have some kind of IoT device in their households
New research by the leading cybersecurity...
The Solution for Privacy and Security in the HealthCare IoT
With the brisk of evolving technology around us, the medical and health care field has witnessed a giant leap in reaching out...
Enea acquires 5G mobile security company
Enea has signed an agreement to acquire AdaptiveMobile Security Ltd, a leading provider of security solutions for mobile networks. The enterprise value...
Business Security Systems. Tech Solutions to Enhance Your Business
Why would anyone break into your business premises, yet you don’t keep any cash or valuable items?
If you...