
If you design embedded devices and rely on secure microcontrollers to protect digital assets and intellectual property (IP), you might be wondering whether the Meltdown and Spectre chip vulnerabilities are affecting them. The answer to this is no, if you’re using Maxim DeepCover secure microcontrollers. Maxim’s secure microcontrollers based on Arm® Cortex®-M and ARM926™processors are unaffected by these hardware-based security vulnerabilities. Also safe from Meltdown and Spectre are the company’s USIP PRO secure microcontrollers based on MIPS processors. Outside of the DeepCover portfolio, Maxim’s MAXQ family of RISC microcontrollers are unaffected, too. Let’s take a closer look at Meltdown and Spectre for a better understanding of how these chips have remained safe from both.
The Meltdown and Spectre vulnerabilities potentially expose critical information stored deep inside computer and embedded systems. Such information could include passwords, proprietary data, and encrypted communications. Both flaws take advantage of the process of speculative execution. Computers utilize speculative execution to determine their next course of action when encountering a test.This process accelerates computer processing time, as the computer speculatively executes the code that it deems most likely to run when confronted with a conditional test. Most of the time, its speculation is correct. To further optimize performance, chips have been designed with the assumption that this speculation process happens without being seen by any outside observers. But this is not the case, as attackers have found ways to see what happens within the speculative window and, thus, manipulate the system. According to a Red Hat blog post, an attacker can trigger certain code sequences that would otherwise not be executed to run speculatively.
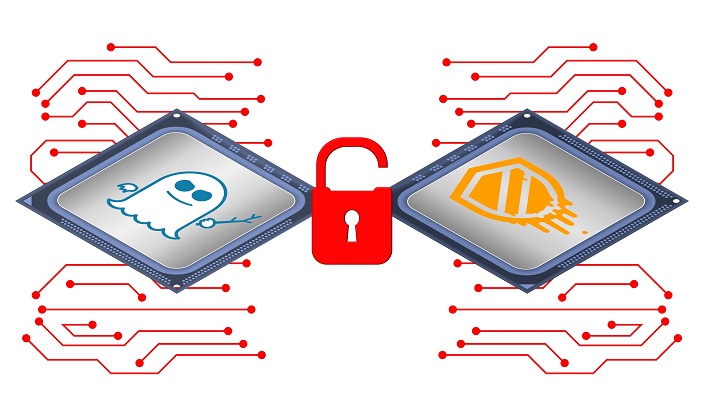
Meltdown impacts only Intel processors. With this flaw, attackers have identified a way to break through the barrier that stops applications from accessing arbitrary locations in kernel memory (where you’d typically find sensitive data in plain format). Spectre affects Intel as well as AMD and Arm processors (including some Cortex-A and Cortex-R processors). This means that mobile devices and many internet of things (IoT) products are affected. Spectre tricks applications into accidentally disclosing information that would otherwise be protected. TechCrunch reports that Meltdown can be halted via kernel page table isolation (essentially a stronger wall around the kernel). Spectre is another story, with TechCrunch noting, “The fact is that the practice that leads to this attack being possible is so hard-wired into processors that the researchers couldn’t find any way to totally avoid it.”
Chipmakers and operating system developers are issuing patches and other updates. Notes TechCrunch, “A more permanent fix will require significant changes across the board—the circuit board, that is. Basic architecture choices that have been baked into our devices for years, even decades, will have to be rethought. It won’t be easy, and it won’t be fun.”
For Arm, only some Cortex-A and Cortex-R processors are affected by Spectre. The Cortex-M and ARM926 processors on which many of Maxim’s secure microcontrollers are based are not impacted. The MAXQ and USIP products do not utilize speculative execution and are, therefore, safe. In summary, Maxim’s secure microcontrollers, which are designed with advanced cryptography and physical security, remain safe choices to protect your designs from physical tampering, reverse engineering, and side-channel attacks.


















