The use of applications and software is almost everywhere in today’s world. It is important to ensure that the activities carried out on these applications are secure and do not put the user’s data at risk. A recent security concern is the ‘Log4J Vulnerability‘ that threatens user privacy. It has led to the corruption of their data and information. Read on to learn more about the concept of Log4J vulnerability and how the problem can be tackled.
What is Log4J?
Developers can log user activities using the Apache Logging Services’ open-source, Java-based Log4J tool. This is a crucial component of the software because it enables the creators to be aware of common occurrences and user behaviors to give their users a more seamless experience. Log4J works as a foundational tool for various services that are used in different fields.
What is Log4J Vulnerability?
One of the most recent issues in Log4J is the Log4J vulnerability or Log4Shell. It enables intruders to access the system. In this manner, they can seize control of the server and even gain access to user data. Additionally, they have remote access to the software code and any private data that belongs to the user, including passwords and login information. Thus, hackers and ransomware gangs are utilizing it. The problem was first identified in December 2021 and is still present.
It is by using a malicious text-based query that hackers cause a log message to be sent. By using Log4J to interpret this query as a command, hackers are able to take over the targeted server.
How To Fix the Log4J Vulnerability?
Since the problem is very common and highly alarming, it is critical to take steps to solve the problem. One way is to update the Log4J version. Apache has made attempts to fix the issue in the recent versions, so it is wiser to keep your version up-to-date. Moreover, users should also start an incident response procedure in order to make sure that no vulnerabilities exist in the application or the system. There should be a thorough check and constant monitoring of server logs to look for any vulnerabilities that may exist.
Multiple tools can be found in the market to scan Log4J vulnerability. It provides a convenient way to detect any such risk. However, users must check the accuracy rates of these tools to ensure that they work in accordance with their needs.
Furthermore, another way is to disable Java Naming and Directory Interface (JNDI). The JNDI plugin allows attackers to enter because of a design flaw. A simple change in a string allows attackers to enter the system. Disabling the JNDI class will prevent any vulnerability in the logged data.
In addition, the latest firewall should be installed to keep the network secure. Incoming and outgoing packets are scanned by firewalls. The latest firewalls will have strict rules over the server. It largely helps prevent attacks that are associated with Log4J vulnerability. These firewalls block attackers’ requests, and this way, most dangers can be avoided.
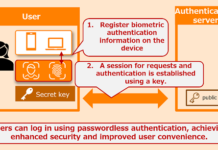
Adding on, multi-factor authentication also provides an enhanced level of security to applications and software. This involves adding a second layer of security by adding biometrics like fingerprint scanning, retina scanning, etc. There can be security questions or a PIN required to enter the system, which makes it difficult for attackers to launch a full-scale attack. Attackers would have to spend more time attempting to enter the system. It can also promptly notify the user of the problem in the meantime, giving the opportunity to take the appropriate corrective action while they still have time. Businesses must also implement stringent VPN policies to minimize data breaches.
It is good to check whether third-party vendors are using Log4J in their applications. There are cases when a user can have all security measures in store but come across hacking via outside sources or third-party integration.
Thus, it is of immense significance for a user to know about this vulnerability because it can be a part of any application or software. This, in turn, puts a lot of information at risk. The seriousness of this problem can be perceived from the fact that defense ministries and officials are also at risk because of this vulnerability, as Log4J services are used everywhere.
Ending Note
Although it can be challenging to identify the Log4J vulnerability, it is necessary to take measures. In order to mitigate the risk and harm brought on by this security issue, many cloud-based services and technologies, including Amazon Web Services (AWS), have incorporated security safeguards.