Security in Internet of Things ecosystem to be of prime focus in 2018
Amid a rise in cyber attacks across the world, ensuring the security of devices linked to the Internet of Things (IoT) ecosystem will be a key focus of companies in 2018, say experts.
The IoT is a growing network of inter-connected devices that can be accessed through the Internet.
"IoT devices have been a cause for concern for consumers. We will...
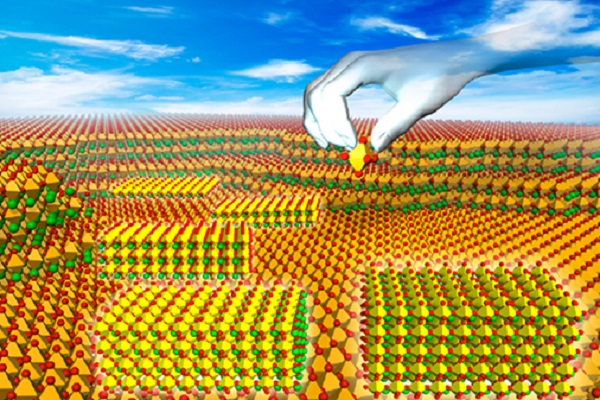
Atomically Thin Perovskites Boost for Future Electronics
WPI-MANA has developed the world's highest performance dielectric nanofilms using atomically thin perovskites. This technology may revolutionize the next-generation of electronics.
This research was conducted by a WPI-MANA research group led by Principal Investigator Minoru Osada and Director Takayoshi Sasaki of WPI-MANA at NIMS. Electronic devices are getting smaller all the time, but there is a limit to how small...
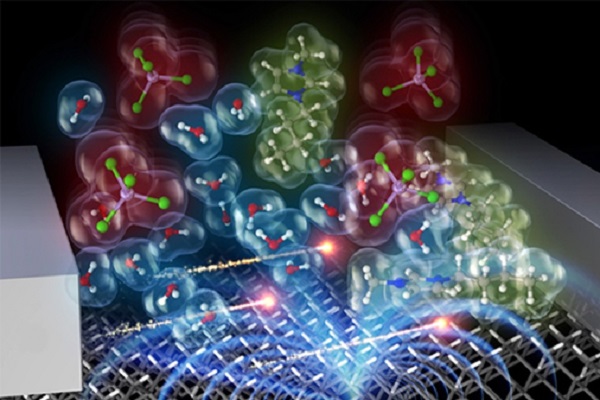
Innovative Transistors Based on Magnetically Induced Movement of Ions
Electrochemical devices find application in many technologies, including batteries, capacitors, sensors, and transistors. For such electrochemical devices to operate, they need an electric field that causes ionic transport and electrochemical processes. This simple but strict rule has long hindered innovation in electrochemistry and related technologies, however, WPI-MANA researchers recently challenged the rule with their development of ‘magnetic control of...
Programmable Logic Controllers (PLCs) and Programmable Automation Controllers (PACs) Manufacturing Companies
Overwhelming rise in global industrial automation expenditure and rise of smart cities has given boost to the intensive PLCs (Programmable Logic Controllers) and sensors industry. PLCs, PACs, sensors network and PLC-controlled implementation for smart homes are among the major growth driving factors of the global market and thus key players in the industry are ready to reap the most...
Role of Operating system in Security
Computer system and software design should address the legitimate security concerns and incorporate appropriate safeguards and mechanisms for enforcement of security policies. On the other hand, extensive security measures can increase cost and restrict the usefulness, user-friendliness, and performance of computer systems. The challenges to system designers are to strike a good balance by making computers effective without compromising...
DATA SECURITY IN THE CLOUD
It has not yet reached epic proportions, but the number of organizations adopting cloud-based technologies is growing dramatically. Organizations of all sizes across industries are turning towards cloud-based infrastructure and cloud computing for better scalability, accessibility and a collaborative work environment. However, after moving to the cloud, many organizations mistakenly assume that it is the role of...
List of Top 10 Electronics connector manufacturers in India
Electronic Connectors are the electro-mechanical devices which are used to connect/ plug or unplug signals and power in wires, boards, Chips and different types of electronic components. Connectors usually desired to join the subsections and disconnect them in future as the need for power inputs, boards or peripheral connections to be replaced. Connectors come in different shapes, sizes and...
Beware when Buying Internet Connected Toys
If you are a technology freak and would like to bring or gift connected devices or toys to your loved ones and kids of your family then think twice. Recently in news, the internet connected toys with camera and location tracking services can be at risk to get hacked. Today, as connected devices are increasing at your...
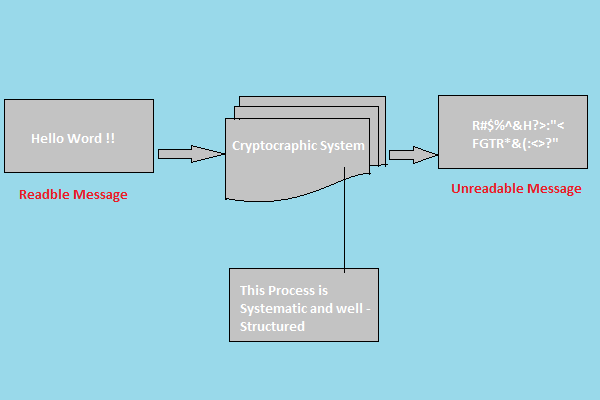
What do you understand by cryptography?
Cryptography is the art and science achieving security by encoding message to make them non readable.
Cryptographic systems are characterised along three independent dimensions
1 The type of operations used for Transforming plaintext to Chiphertext:
All encryption algorithm are based on two general principals solution, in which each element in the plaintext (bit, letter, group of bits or letters) is mapped in to...
Control Strategies used in Artificial Intelligence to reach the solution
Control Strategy in Artificial Intelligence scenario is a technique or strategy, tells us about which rule has to be applied next while searching for the solution of a problem within problem space. It helps us to decide which rule has to apply next without getting stuck at any point. These rules decide the way we approach the problem and...