5 Ways Internet of Things Transforms Your Home
In case you are still in doubt, you are living in what is called the “golden age of technology.” For the past few years, the world has come from working with bulky corded phones to pocket-sized computers, and they are capable of carrying out dozens of communication functions simultaneously. If the smartphone was the biggest tech development...
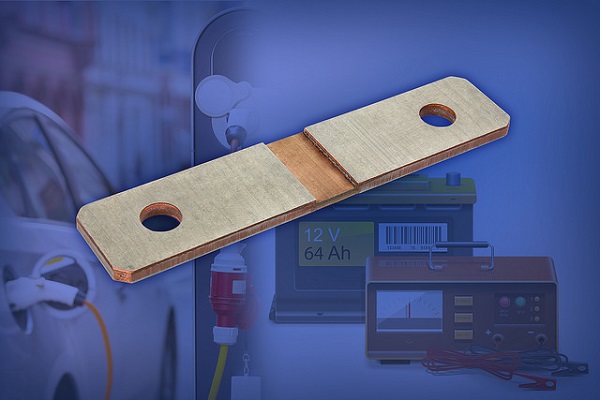
Vishay Intertechnology Automotive Grade Power Metal Strip Battery Shunt Resistor Offers Improved Accuracy, Corrosion Protection
Vishay Intertechnology, Inc. (NYSE: VSH) today announced a new Automotive Grade Power Metal Strip battery shunt resistor that offers a 36 W power capacity in the 8518 case size with tin plating on the terminals. Featuring extremely low resistance values down to 50 µΩ, the Vishay Dale WSBS8518...14 will lead to increased accuracy and lower costs compared to Hall...
IoT Asia 2018 – Internet of Things Asia 2018 Dates and Location
IoT Asia 2018 is one of the most attended and biggest expo on Internet of Things and connected world in Singapore. After the immense success in earlier edition of exhibition, exhibitor is planning to add more features to the show. Exhibitors from all over the Asia and world will participate to showcase their product in the upcoming Internet of...
Hindustan Zinc plans solar power projects worth Rs425 crore by next year
New Delhi: Hindustan Zinc on Sunday said its 15 MW solar projects in Rajasthan will get commissioned this month, and it is also planning to invest Rs425 crore for 85 MW power plants by next year.
“We are in the process of putting up 15 MW (rooftop solar power plants) which will get commissioned before 31 March. We would be...
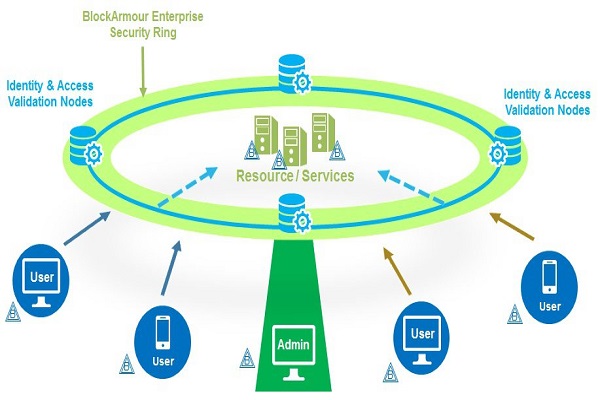
Indian Startup Develops a Next-Gen Cybersecurity Solution on the Blockchain
A new innovative prototype startup powered by blockchain technology for cybersecurity has recently launched in India aimed at curbing the global phenomenon of cybercrime.
Mumbai-based Block Armour was thought up by Narayan Neelakantan, former CISO and Head of IT Risk and Compliance with India’s National Stock Exchange (NSE) and Floyd DCosta, who has a background in management consultancy and spent...
Anritsu Introduces MT8862A Wireless Connectivity Test Set
Tokyo, March 27, 2017 - Anritsu Corporation (President Hirokazu Hashimoto) introduced company’s new MT8862A instrument with industry-first Network Mode for evaluating IEEE802.11ac WLAN devices. This new model strengthens the company’s products for testing WLAN equipment, which is expected to see good growth in line with the expanding IoT market.
With built-in communications protocols*1 supporting IEEE802.11ac/n/a/g/b as standard, the MT8862A uses...
LANXESS_New sustainability in the tanning process
Cologne – Specialty chemicals company LANXESS is leading a research and development project to investigate an innovative technology for a new recycling concept in leather manufacturing. Under the title “Resource-efficient manufacturing of leather chemicals” (ReeL), LANXESS Leather business unit is working with the Leverkusen-based research institute INVITE to develop a modular pilot plant that can use shavings previously disposed...
Comprehensive portfolio of advanced Gigabit Ethernet products offers ease-of-design
27 March 2017, New Delhi, — A new portfolio of 48Gigabit Ethernet chips featuring advanced capabilities, certified compliance, comprehensive software support and copy-ready evaluation tools is now available from Microchip Technology Inc., a leading provider of microcontroller, mixed-signal, analog and Flash-IP solutions. The new suite of products, known together as GigEpack, aims to reduce complexity and remove barriers in...
BOLSTERING NATIVE ENCRYPTION WITH CENTRALISED KEY MANAGEMENT
Authored by Rahul Kumar, Country Manager, WinMagic
With native encryption being factory installed on nearly all endpoints – like desktops, laptops and tablets – it has quickly become the default encryption solution for IT managers. Technologies like BitLocker and FileVault2 are a great start at improving data security. But to expose the full capability of the native encryption, enterprises truly...
A Game of Cat and Mouse:Dynamic IP Address and Cyber Attacks
March 2017 - In recent years, cyber attackers have adopted a new, more surreptitious operational mandate; one that employs a set of strategies and technologies that dramatically complicate the detection process. At the forefront of these rogue like tactics are serving up dynamic IP addresses.
In general, dynamic IP attacks target Layer 7, the application layer. Using real IP addresses,...