Fully Configurable Microcontroller-based CEC1736 Trust Shield family by Microchip
As the market need for security evolves, platforms must also evolve quickly to defend against cyber attacks during start-up, real-time and system...
STMicroelectronics join hands with Microsoft for Highly Secure IoT Devices
Joint efforts deliver Microsoft Azure IoT cloud reference implementation integrating Arm® trusted firmware and based on STM32U5 IoT discovery kit
Types Of Proxies And Their Uses
Proxy servers are believed to be in high demand these days, as many homeowners prioritize privacy in the face of rising cybersecurity...
Variscite Enables Over-the-Air Updates to Enhance IoT and Edge Security
Variscite, a leading System-on-Module designer and manufacturer, announced today it has enhanced security options for IoT and edge devices built with Variscite...
Industry’s First Broad-Scale Cloud SaaS Solution to Transform Chip Development Landscape
Single-Source Model for EDA & Microsoft Azure Infrastructure Delivers Flexibility with Pay-Per-Use Approach for Demanding Chip Design & Verification Needs
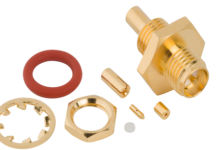
Add Security & Flexibility to WI-FI Devices with Amphenol RF RP-SMA JACKS Connectors
Amphenol RF expands its reverse polarity SMA portfolio with additional straight jacks designed for use with flexible micro-coax cable types with tamper-resistant...
World’s first TPM with a PQC-protected firmware update mechanism
Quantum computing is expected to have a significant impact on cybersecurity, specifically on the confidentiality of encrypted data and on the integrity...
Landitec launched brand new solutions for ideal Network Security & Performance
By launching two new scope7 network appliances, the German VAD of network equipment Landitec extends the product range of its own brand for state-of-the-art...
Scalable Digital Certificate Management System for IoT Devices
u-blox IoT certificate manager automatically renews device credentials according to industry requirements to ensure futureproof protection
u-blox has announced...
Top 6 Nord Security highlights of 2021
Find out about the company’s biggest moments of this year
As 2021 is coming to an end, we at...