32-Bit MCU for Bluetooth 5.0 with Enhanced Security & Privacy
Renesas Electronics introduced the RX23W – a 32-bit microcontroller (MCU) featuring Bluetooth® 5.0 for IoT endpoint devices such as home appliances and...
Infineon’s 40nm Generation of Security Chip Solutions
Infineon Technologies AG sets another milestone in smart card innovation. Its new 40nm generation of security chip solutions – the SLC3x – is based...
What is SSL, how does it work?
If you run a website or blog, first of all you should make
sure that your website is safe and no one can...
“AuthConductor V2” takes Biometric Authentication to the Next Level
Fujitsu launches sales of the "FUJITSU Security Solution AuthConductor V2" which uses various authentication methods, including palm vein authentication, to deliver comprehensive...
SECORA ID solution: security chip with software for eID documents
To address the evolving needs of Electronic identification documents (eID) market in a fast and flexible manner, Infineon Technologies has developed...
AI & 5G makes enterprises more vulnerable to attack: A Study
More than 80% of cybersecurity and risk leaders in a new global survey say the technologies could make enterprises more vulnerable to...
PIN vs. password: which one is more secure?
As users of this digital age, we have many different choices. You can enable or disable web cookies, depending on how much...
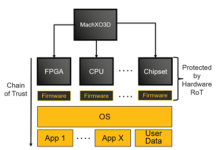
Lattice MachXO3D Secure Control FPGA Receives Security Certification from NIST
Lattice Semiconductor MachXO3D FPGAs for secure system control received the National Institute of Standards and Technology's (NIST) Cryptographic Algorithm Validation Program (CAVP)...
GF brings protection against physical tampering & attacks on cellular IoT devices
GLOBALFOUNDRIES (GF) is working with Arm to offer secure system-on-chip (SoC) solutions on GF’s 22FDX platform, based on FD-SOI, for cellular IoT...
Next-Generation Hardware-Based Cybersecurity Products
UltraSoC announced next-generation hardware-based cybersecurity products that can be used to detect, block and record cyber-attacks in a broad range of applications –...