On October 16th, a research paper titled “Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2” was published in the industry. Taking immediate action Tenda strictly analyzed and tested our released products and the corresponding software at once, then ultimately confirmed that the bugs had no effect on Tenda’s products. Please be assured to purchase and use our products.
Detailed statements are as follows:
Judging from the reported bugs, attacks are mainly on clients. Attacker realizes packets eavesdropping and injection and implements MITM attacks by inducing client users to load the key that is being used currently. Tenda wireless products are not influenced by the bugs when products work in router mode or AP mode (as authenticators for four-way handshakes). After repeated analysis, demonstration, and actual tests, we finally confirm that Tenda wireless products are also not influenced by the bugs when products work in WISP mode or Universal repeater mode (as supplicants for a four-way handshake). You can be relieved to use our products. Authentication on adapters is achieved by the operating system, so please update windows system patches immediately. By the way, you are not required to update the adapter drivers.
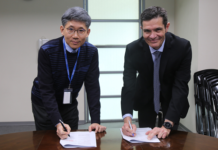
“As soon as we got aware of Key Reinstallation Attacks, our team in HQ got their heads together and started testing and analyzing our products for same, Considering the huge number of customers we serve, it was our duty to solve their concern of this breach, and I’m happy to share that, our team was able to research and study the paper thoroughly and released with the assured statement above” Said Mr Frank Rao, G.M. India & SAARC, Tenda Technologies.