How AI Finds Big Value in Big Data
Bots can augment human interaction, create greater business efficiencies, and remove friction from customer interactions. It’s a market that has already rolled up $24 billion in funding for...
10 Uses for Artificial Intelligence-Powered Smartphones
Artificial intelligence (AI) features will become a critical product differentiator for smartphone vendors that will help them to acquire new customers while retaining current users, according to...
Vulnerability Management: A guide for buyer
Exploiting weaknesses in browsers, operating systems, and other third-party software to infect end user systems is a common initial step for security attacks and...
Indian INCs Look at Investment in Security Big Time in 2018
2017 will undoubtedly be considered as ‘Year of ransomware’, the year when the global security landscape was forever changed by attacks like WannaCry and...
DATA SECURITY IN THE CLOUD
It has not yet reached epic proportions, but the number of organizations adopting cloud-based technologies is growing dramatically. Organizations of all sizes...
Control Strategies used in Artificial Intelligence to reach the solution
Control Strategy in Artificial Intelligence scenario is a technique or strategy, tells us about which rule has to be applied next while searching for...
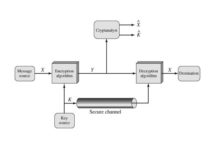
What is the Conventional Encryption Model?
Symmetric encryption is also referred to as conventional encryption or single-key encryption. It was the only type of encryption in use prior to the...
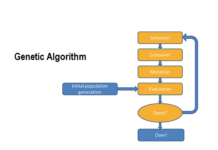
Applications of Genetic Algorithm
The Key of the success in Genetic Algorithm applications are effective GA representation and meaningful fitness evaluation. The demand of Genetic Algorithm comes from...
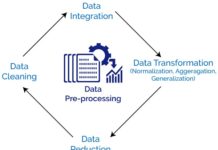
What do you mean by Data preprocessing and why it is needed?
Data Preprocessing is a technique that used to improve the quality of the data before applied mining, so that data will lead to high...
10 Ways you can be Hacked – Browse Secure
Social Engineering: One of the world’s most famous hacker Kevin Mitnick explained in his book “The Art of Deception” the power of social engineering...