ETERNITY NENXIP50 – The Complete IP PBX Solution for a minimal enterprise
“Communication is the key” - probably, to a lot of things including the efficient and productive growth at a firm. If managed...
Landitec launched brand new solutions for ideal Network Security & Performance
By launching two new scope7 network appliances, the German VAD of network equipment Landitec extends the product range of its own brand for state-of-the-art...
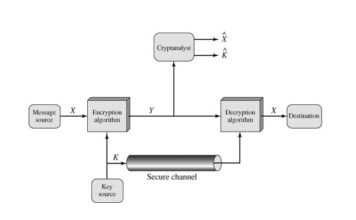
CryptoAuthentication Device for Secure Connected Systems
Mouser Electronics is now stocking the ATECC608B CryptoAuthentication device from Microchip Technology. Delivering ultra-secure cryptographic elements that enable more secure connected systems,...
RZ/G Linux Platform Solution to Protect Industrial Control Systems from Cyberattacks.
Renesas Electronics announced plans to release a security solution based on the Renesas RZ/G Linux Platform that will reduce the amount of time required...
World’s first Smart Mobile Device Vendor to obtain Privacy Protection Certification
On April 8, 2020, Huawei released P40 series in its spring online launch event, in which Richard Yu, CEO of Huawei's Consumer...
Enea acquires 5G mobile security company
Enea has signed an agreement to acquire AdaptiveMobile Security Ltd, a leading provider of security solutions for mobile networks. The enterprise value...
Opportunities Abound in Embedded Security Market in Line with Rising Sophistication of Cyberattacks
Fairfield Market Research finds that, by 2026, the total market share of the global embedded security market is set to reach US$10...
Microchip Technology Introduces ECC608 TrustMANAGER with Kudelski IoT keySTREAM
As the world comes to rely on interconnected IoT systems—for everything from household items like smart thermostats, virtual assistant technology and digital...
Cloud Hosted Services: Some security considerations
A multi-cloud approach enables organizations to move application services to various public cloud providers depending on the desired service level and price...
Open-Source Embedded Security Solution
A few lines of code embedded in the firmware is all it takes to offer multi-layer, virtually impenetrable protection for the world’s...