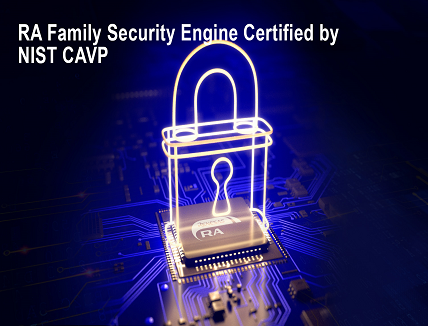
Renesas Electronics Corporation announced that the security engine of its RA Family of 32-bit Arm® Cortex®-M microcontrollers (MCUs) has been certified by the National Institute of Standards and Technology (NIST) Cryptographic Algorithm Verification Program (CAVP). The drivers to utilize the certified SCE9 Protected Mode are included in the RA Family Flexible Software Package (FSP) v3.6.0 and later.
The Renesas RA6M4, RA6M5, RA4M2, and RA4M3 MCU Groups all received NIST CAVP certification of a comprehensive suite of cryptographic algorithms, including multiple modes of Advanced Encryption Standard (AES), hashing, Rivest Shamir Adleman (RSA) and Elliptic Curve Cryptography (ECC) key generation and authentication, Key Agreement Schemes, and Deterministic Random Bit Generator (DRBG). NIST CAVP certification provides independent verification of the correct implementation of the cryptographic algorithms, which is vital to ensure connectivity interoperability.
Renesas announced last year that RA devices received both PSA Certified Level 2 and Security Evaluation Standard for IoT Platforms (SESIP) certifications.
“With CAVP certification, in conjunction with the existing SESIP1 and PSA Certified Level 2, Renesas provides the industry’s most comprehensive IoT security solutions,” said Roger Wendelken, Senior Vice President in Renesas’ IoT and Infrastructure Business Unit. “Customers in a broad range of connected application segments can implement the RA family with supreme confidence that their data will be secure.”
Renesas’ unique integrated security architecture provides a time and energy-efficient solution with unlimited secure key storage. An independent evaluation to compare SCE9 Protected Mode operation to a selection of industry-leading secure elements was recently completed. “The SCE9 doesn’t just pack a significant amount of cryptographic compute power, but getting rid of a serial interface (usually I2C) to an externally connected device provides various advantages, said Mario Noseda from Zurich University of Applied Sciences, School of Engineering. “The high clock frequency of the internal data bus greatly reduces the data transmission time between the MCU and the SCE9. But even more important is the complete elimination of a point of attack, which is a huge selling point for an MCU containing the SCE9.” A white paper detailing the evaluation is available at htpps://digitalcollection.zhaw.ch/bitstream/11475/23809/3/2021_Noseda-Ruest_Crypto-acceleration-for-IoT.pdf.
Proper handling of cryptographic keys is vital to maintaining the integrity of a secure product. The new Security Key Management Tool provides a straight-forward mechanism for preparing keys for secure installation and updates, supporting development, production provisioning, and key updates for products in the field. The GUI interface is designed to assist developers, particularly those new to security solutions, to create prototypes and proofs-of concepts with test keys. The command line interface coordinates across multiple developers and supports production key management of key provisioning and update. Downloadable Application Projects demonstrate how to perform secure key installation and updates for both development and production using the available Renesas tools. Find the complete list of security-orientated software, tools, and solutions at www.renesas.com/iot-security.
In addition to these widely recognized industry certifications, Renesas RA MCUs offer customers the ultimate IoT security by combining Secure Crypto Engine IP with NIST CAVP certifications on top of Arm TrustZone® for Armv8-M. RA Family devices incorporate hardware-based security features from simple AES acceleration to fully integrated crypto subsystems isolated within the MCU. The Secure Crypto Engine provides symmetric and asymmetric encryption and decryption, hash functions, true random number generation (TRNG), and advanced key handling, including key generation and MCU-unique key wrapping. An access management circuit shuts down the crypto engine if the correct access protocol is not followed, and dedicated RAM ensures that plaintext keys are never exposed to any CPU or peripheral bus.