Indian INCs Look at Investment in Security Big Time in 2018
2017 will undoubtedly be considered as ‘Year of ransomware’, the year when the global security landscape was forever changed by attacks like WannaCry and...
DATA SECURITY IN THE CLOUD
It has not yet reached epic proportions, but the number of organizations adopting cloud-based technologies is growing dramatically. Organizations of all sizes across industries...
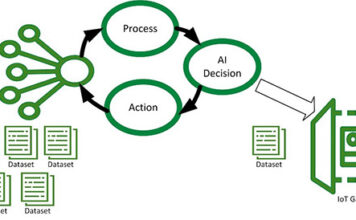
Control Strategies used in Artificial Intelligence to reach the solution
Control Strategy in Artificial Intelligence scenario is a technique or strategy, tells us about which rule has to be applied next while searching for...
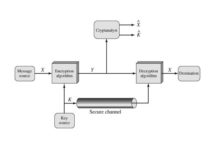
What is the Conventional Encryption Model?
Symmetric encryption is also referred to as conventional encryption or single-key encryption. It was the only type of encryption in use prior to the...
Applications of Genetic Algorithm
The Key of the success in Genetic Algorithm applications are effective GA representation and meaningful fitness evaluation. The demand of Genetic Algorithm comes from...
What do you mean by Data preprocessing and why it is needed?
Data Preprocessing is a technique that used to improve the quality of the data before applied mining, so that data will lead to high...
10 Ways you can be Hacked – Browse Secure
Social Engineering: One of the world’s most famous hacker Kevin Mitnick explained in his book “The Art of Deception” the power of social engineering...
LiFi technology – A new wireless network technology
Most of us are familiar with Wi-Fi (Wireless Fidelity) which uses 2.4 to 5 GHz RF to deliver wireless Internet access around our homes,...
AC/DC LED Drivers with Constant Current or Constant Voltage Mode
Constant Current Mode
The drivers are equipped with a current limiting circuit set to the maximum rated current for the specific driver model. As a...
How IoT is Transforming Home Automation
Today in the headway of Automation innovation, life is getting simpler and less demanding in all spheres. Home automation is a modern technology that...