Protecting Sensitive Data: The Death of an SMB
Due to this lack of care, 61% of data breach victims are specifically small businesses according to service provider Verizon’s 2018 Data Breach Investigations.
Although...
Access to Applications Based on a “ Driving License” Model
In today’s dynamic times, more and more countries are modifying their policies with a new “driving license” model. With a classic license model, drivers...
Skybox Security Signs RAH Infotech as National Distributor in India
Skybox Security a global leader in cyber security management; today announced that it has signed an agreement with RAH Infotech, India's fastest growing value-added technology distributors, to...
Secure Server Data with Winmagic Server Encryption Solution
WinMagic, an award-winning encryption and key management solution provider, is today encouraging enterprises to adopt server encryption as part of their regular data security...
Infineon and IDEX Biometrics: Working together to advance biometric card landscape
Working together to advance the biometric card landscape: Infineon Technologies AG and IDEX Biometrics, the leading provider of advanced fingerprint identification and authentication solutions...
EEMBC’s SecureMark-TLS focuses on Transport Layer Security protocol for IoT edge nodes ...
EEMBC, an industry consortium that develops benchmarks for embedded hardware and software, announced that its SecureMark -TLS benchmark is now available for licensing. Part...
Infineon Open source software stack for TPM 2.0 securing industrial & automotive applications
Infineon Technologies AG has enabled a new open source software stack. It makes work easier for developers who want to use the Trusted Platform...
Microchip 32-bit MCU with Chip-level Security & Arm TrustZone Technology to Create Secured IoT...
With the booming growth of Internet of Things (IoT) endpoints, security is sometimes an afterthought for many designers, increasing the risk of exposing intellectual...
Synopsys DesignWare Security IP for Drone SoC selected by Artosyn
DesignWare tRoot Hardware Secure Module with Root of Trust protects sensitive information within an SoC
Multi-stage secure boot validates software and data integrity...
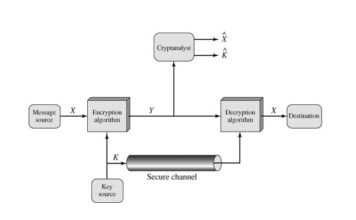
Blockchain Security 2Go Starter Kit for Secure & Friendly Digital Transactions
Digital transactions require secured yet user-friendly solutions. This applies all the more so for Blockchain applications where the user credentials are one of the...